Selection & Interfaces
Chapter 5 — Core Product Introduction, Interface Logic, and Feature Comparison
5.1 Core Product Introduction
Router selection for security-focused deployments must consider not only throughput and port density, but also the breadth and depth of security feature support. Key security-relevant capabilities include hardware-accelerated ACL and uRPF processing, CoPP/CPP support with per-class rate limiting, routing protocol authentication (MD5, SHA-256, TCP-AO), management plane isolation (dedicated management VRF, OOB port), AAA integration (TACACS+, RADIUS), secure boot and image verification, and NETCONF/YANG or REST API support for automated compliance checking.
The three product tiers shown below represent the typical selection range for enterprise and service provider deployments. Branch routers provide essential security features in a compact, cost-effective form factor suitable for ZTP deployment. Edge routers provide full security feature sets with hardware-accelerated processing suitable for high-throughput WAN and DC edge deployments. Service provider chassis routers provide carrier-grade scale, redundancy, and feature depth for the most demanding environments.

| Feature | Branch Router (ISR-class) | Edge Router (ASR-class) | SP Chassis (NCS/CRS-class) |
|---|---|---|---|
| Throughput | Up to 2 Gbps | Up to 400 Gbps | Up to 160 Tbps |
| WAN Interfaces | 4x GE, optional SFP | Multiple SFP+/QSFP modules | 100G/400G line cards |
| Mgmt Port | 1x GE OOB | 1x GE OOB dedicated | Dedicated mgmt module |
| Routing Protocol Auth | MD5, SHA-256 | MD5, SHA-256, TCP-AO | MD5, SHA-256, TCP-AO, RPKI |
| CoPP/CPP | Software CoPP | Hardware CoPP | Carrier-grade CPP |
| uRPF | Software uRPF | Hardware uRPF | Hardware uRPF at line rate |
| VRF Support | Up to 32 VRFs | Up to 4,096 VRFs | Up to 64,000 VRFs |
| AAA Integration | TACACS+, RADIUS | TACACS+, RADIUS, LDAP | TACACS+, RADIUS, LDAP, PKI |
| Secure Boot | Optional | Standard | Standard + TPM |
| Automation API | NETCONF/YANG | NETCONF/YANG, REST | NETCONF/YANG, REST, gRPC |
| Redundant PSU | Optional | Standard | N+1 redundant |
| Typical Use Case | Branch, small office | WAN Edge, DC Edge, Campus Core | SP Edge, large DC, carrier |
5.2 Interface Logic & Port Assignment
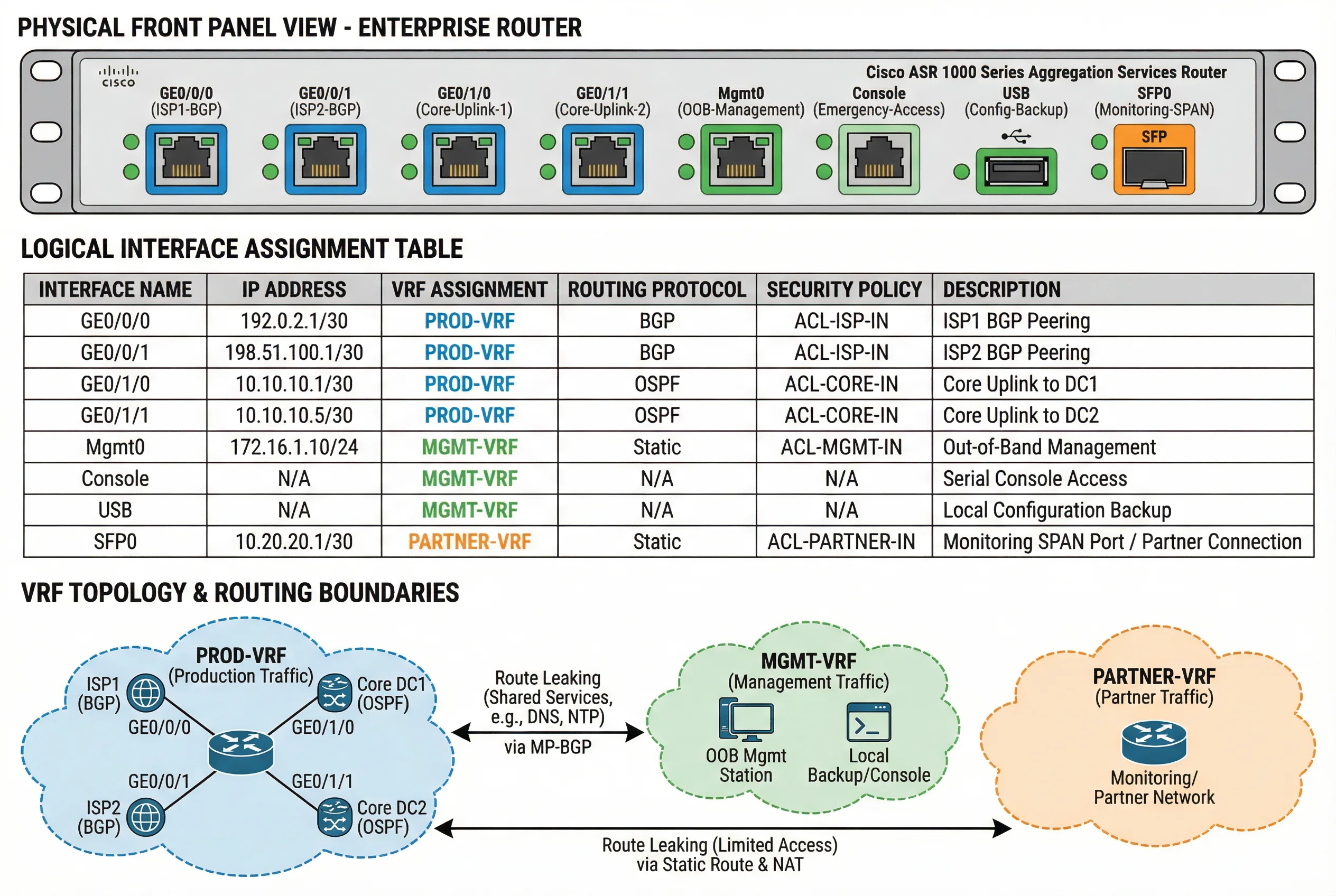
Proper interface assignment is a foundational security control: each interface must be assigned to the correct VRF, have the appropriate security policy applied, and be documented with its logical role. The interface logic diagram below shows the physical front panel layout, the logical interface assignment table, and the VRF topology with routing boundaries. This three-layer view enables engineers to understand both the physical reality and the logical security model simultaneously.
The VRF topology shows three routing domains: PROD-VRF for production traffic, MGMT-VRF for management traffic, and PARTNER-VRF for partner/extranet traffic. Route leaking between VRFs is strictly controlled via MP-BGP with explicit import/export policies, ensuring that only specifically permitted routes cross VRF boundaries.
Interface Security Policy Matrix
| Interface Type | VRF | Ingress ACL | Egress ACL | uRPF Mode | Routing Protocol | Auth Required |
|---|---|---|---|---|---|---|
| ISP Peering (eBGP) | PROD-VRF | ACL-ISP-IN (strict) | ACL-ISP-OUT | Loose | eBGP | TCP-AO / MD5 |
| Core Uplink (iBGP) | PROD-VRF | ACL-CORE-IN | ACL-CORE-OUT | Strict | OSPF + iBGP | OSPF SHA-256 |
| DC Server Segment | PROD-VRF or Tenant VRF | ACL-DC-IN | ACL-DC-OUT | Strict | OSPF | OSPF SHA-256 |
| Management (OOB) | MGMT-VRF | ACL-MGMT-IN (ops subnet only) | ACL-MGMT-OUT | N/A | Static | SSH v2 + AAA |
| Partner Extranet | PARTNER-VRF | ACL-PARTNER-IN (per partner) | ACL-PARTNER-OUT | Strict | eBGP | TCP-AO per partner |
| Console | MGMT-VRF | N/A (physical) | N/A | N/A | N/A | AAA + local fallback |
5.3 Core Product Feature Table
The following comprehensive feature table covers all security-relevant capabilities across the three product tiers, organized by functional category. This table serves as the primary reference for procurement specifications and acceptance testing criteria. Each feature is rated as Supported (full hardware implementation), Partial (software implementation or limited scale), or Not Supported.
| Category | Feature | Branch (ISR) | Edge (ASR) | SP Chassis | Notes |
|---|---|---|---|---|---|
| Management Plane | Dedicated OOB Port | Yes | Yes | Yes | Physical separation |
| Management VRF | Yes | Yes | Yes | Logical separation | |
| SSH v2 Only | Yes | Yes | Yes | Telnet must be disabled | |
| HTTPS / TLS 1.2+ | Yes | Yes | Yes | HTTP must be disabled | |
| AAA | TACACS+ / RADIUS | Yes | Yes | Yes | Both protocols supported |
| Command Authorization | Yes | Yes | Yes | Per-command TACACS+ | |
| PKI / Certificate Auth | Partial | Yes | Yes | Full PKI on Edge+ | |
| Routing Security | BGP TCP-AO | Partial | Yes | Yes | MD5 fallback on Branch |
| RPKI Origin Validation | No | Yes | Yes | Edge+ only | |
| OSPF SHA-256 Auth | Yes | Yes | Yes | All tiers | |
| Control Plane | Hardware CoPP | Partial | Yes | Yes | Software CoPP on Branch |
| Per-class Rate Limiting | Yes | Yes | Yes | All tiers | |
| Data Plane | Hardware uRPF | Partial | Yes | Yes | Software uRPF on Branch |
| Hardware ACL | Partial | Yes | Yes | TCAM-based on Edge+ | |
| Automation | NETCONF/YANG | Yes | Yes | Yes | All tiers |
| gRPC Telemetry | No | Partial | Yes | Full support on SP Chassis |