Supporting Equipment Requirements
Chapter 7 — Integrated Supporting Infrastructure for Secure Router Deployment
A secure router deployment requires more than just the router itself. The surrounding infrastructure — management switches, terminal servers, AAA servers, NTP servers, monitoring platforms, and physical security hardware — is equally critical to the overall security posture. This chapter defines the complete set of supporting equipment required for a production-grade secure router deployment, organized by functional category and integrated into a single reference diagram.
7.1 Integrated Supporting Equipment Overview
The integrated diagram below shows all supporting equipment categories in a single view, with color-coded connections indicating the type of traffic flowing between each component. This integrated perspective is essential for understanding the dependencies between components and ensuring that no single supporting device becomes a bottleneck or single point of failure for the entire security infrastructure.
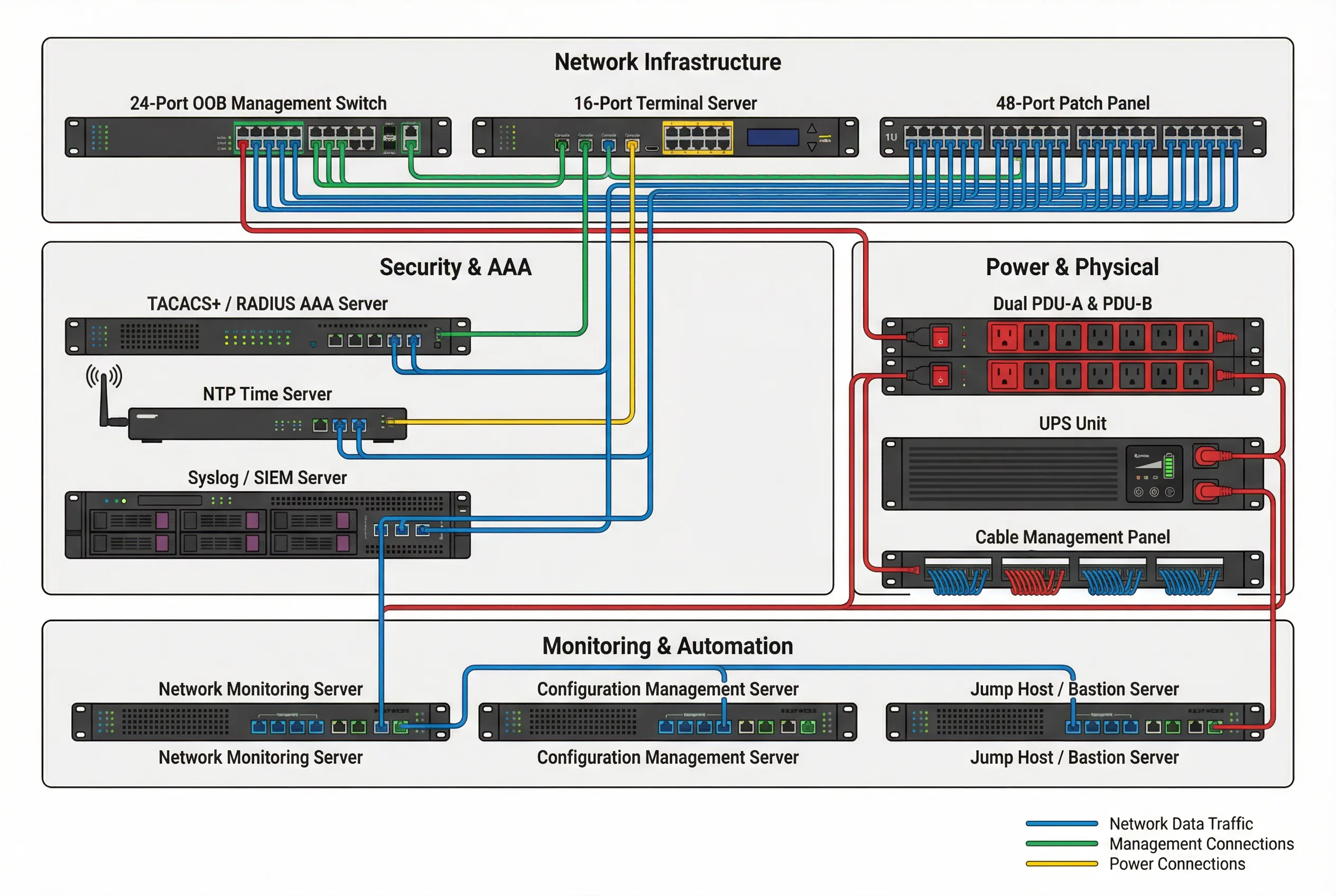
The diagram organizes supporting equipment into four functional zones: Network Infrastructure (OOB switch, terminal server, patch panel), Security & AAA (AAA server, NTP server, SIEM), Power & Physical (PDUs, UPS, cable management), and Monitoring & Automation (monitoring server, config management, jump host). Each zone is interconnected with appropriate color-coded links showing network data, management, and power connections.
7.2 Network Infrastructure Components
| Component | Specification | Security Requirement | Redundancy |
|---|---|---|---|
| OOB Management Switch | 24-port managed switch; dedicated to management traffic only; VLAN-capable; SNMPv3 monitoring | No production traffic; port security; 802.1X authentication for connected devices; ACL on all ports | Dual-homed to two OOB switches for redundancy |
| Terminal Server | 16-port async console server; SSH access to all console ports; session logging; break-in detection | SSH-only access; AAA authentication; all console sessions logged; idle timeout 5 minutes | Single terminal server acceptable if OOB switch is redundant |
| Patch Panel | 48-port Cat6A patch panel; labeled at both ends; cable management rings; color-coded by function | Physical access control to patch panel; tamper-evident seals on unused ports; documentation required | N/A — passive component |
7.3 Security & AAA Infrastructure
| Component | Specification | Security Requirement | Redundancy |
|---|---|---|---|
| AAA Server (TACACS+/RADIUS) | Dedicated AAA appliance or VM; TACACS+ and RADIUS support; LDAP/AD integration; MFA support; command authorization | Hardened OS; encrypted storage; audit logging; access restricted to OOB network; regular backup | Primary + secondary AAA server; automatic failover; local fallback on router |
| NTP Time Server | Stratum-1 or Stratum-2 NTP server; GPS or atomic clock reference preferred; NTP authentication support | NTP authentication (MD5 or SHA-1) required; access restricted to OOB network; no public NTP servers | Primary + secondary NTP server; router falls back to secondary if primary unreachable |
| Syslog / SIEM Server | Centralized syslog collector; SIEM correlation engine; real-time alerting; 12-month retention; encrypted storage | Immutable log storage; access restricted to security team; TLS-encrypted syslog transport; integrity checking | Clustered SIEM with replication; backup to secondary site |
7.4 Power & Physical Infrastructure
| Component | Specification | Security Requirement | Redundancy |
|---|---|---|---|
| Dual PDU (PDU-A / PDU-B) | Rack-mount PDU; metered and switched; remote power cycling capability; C13/C19 outlets; 20A/30A circuit | PDU access restricted to authorized personnel; remote power cycling requires MFA; power cycle events logged | PDU-A on Circuit-A; PDU-B on Circuit-B; never share circuits |
| UPS Unit | 2U rack-mount UPS; minimum 10-minute runtime at full load; SNMP monitoring; automatic shutdown capability | UPS management interface on OOB network; SNMPv3 monitoring; battery status alerts | UPS on each PDU circuit; generator backup for extended outages |
| Cable Management | 1U horizontal cable management panels; vertical cable managers; color-coded cables; labeled at both ends | Proper cable management prevents accidental disconnection; enables quick identification during incidents | N/A — passive component |
7.5 Monitoring & Automation Infrastructure
| Component | Specification | Security Requirement | Redundancy |
|---|---|---|---|
| Network Monitoring Server | SNMPv3 polling; ICMP reachability; interface utilization; BGP session state; CPU/memory trending; alerting | Read-only SNMPv3 credentials; monitoring traffic on OOB network; alert thresholds documented and reviewed quarterly | Primary + secondary monitoring server; alert routing to multiple channels |
| Configuration Management Server | Automated config backup (every 4 hours); config diff detection; compliance checking; rollback capability; version control | Config backups encrypted at rest; access restricted to automation service account; all changes logged; diff alerts to security team | Config backups replicated to secondary site; version control with full history |
| Jump Host / Bastion Server | Hardened Linux server; SSH proxy; MFA enforcement; session recording; privileged access management (PAM) integration | No direct SSH to routers from non-OOB networks; all sessions proxied through jump host; session recording mandatory; idle timeout 5 minutes | Primary + secondary jump host; automatic failover |
7.6 Supporting Equipment Sizing Guide
The table below provides sizing guidance for supporting equipment based on the number of routers being managed. These are minimum recommendations; actual sizing should account for growth projections and peak load scenarios.
| Router Count | OOB Switch Ports | Terminal Server Ports | AAA Server Capacity | Syslog Storage (90 days) | Config Backup Storage |
|---|---|---|---|---|---|
| 1–10 routers | 24-port switch | 16-port terminal server | Single AAA server (VM) | ~50 GB | ~10 GB |
| 11–50 routers | 48-port switch | 32-port terminal server | Primary + secondary AAA | ~250 GB | ~50 GB |
| 51–200 routers | Stack of 48-port switches | 64-port terminal server | AAA cluster (3 nodes) | ~1 TB | ~200 GB |
| 200+ routers | Dedicated OOB network | Multiple terminal servers | Enterprise AAA cluster | >5 TB (SIEM) | >1 TB (version control) |