Router Security Configuration
Design Guide
A comprehensive, implementable security configuration baseline for enterprise and service-provider routers. Covering Management Plane, Control Plane, and Data Plane hardening — driven by minimal exposure, least privilege, auditability, and recoverability principles.
System Overview
This guide defines an implementable security configuration baseline for routers, centered on the three planes of a router: Management Plane, Control Plane, and Data Plane, and driven by the principles of minimal exposure, least privilege, auditability, and recoverability. The scope covers enterprise and service-provider style routers acting as WAN edge, DC edge, campus core/aggregation, and branch gateways.
It includes configuration objectives, control intent, verification points, and acceptance criteria that can be used directly for procurement, implementation, delivery, and operations. In-scope areas include secure administrative access, AAA and privileged role separation, secure management services, logging and time synchronization, routing protocol hardening (authentication, neighbor whitelisting, anti-route-injection controls), control-plane protection and rate limiting, data-plane boundary filtering, anti-spoofing/source validation, and configuration backup/rollback workflows.
Key dependencies for this guide include AAA servers (RADIUS/TACACS+), NTP, syslog/SIEM, jump host/VPN, PKI (optional but recommended), and a configuration backup system. The guide produces hardened configuration templates, device onboarding checklists, verification test plans, and runbooks for backup/restore and emergency access.
System Architecture
The overall architecture separates operational responsibilities across three layers: the Ops layer provides identity (AAA/MFA), telemetry (logs/NTP), and change control (backup/versioning); the Router layer enforces plane separation and protections (management lockdown, routing hardening, CoPP/CPP, data-plane filtering); and the Network Edge layer applies external boundary policies (route policies, ingress/egress ACL, anti-spoofing).
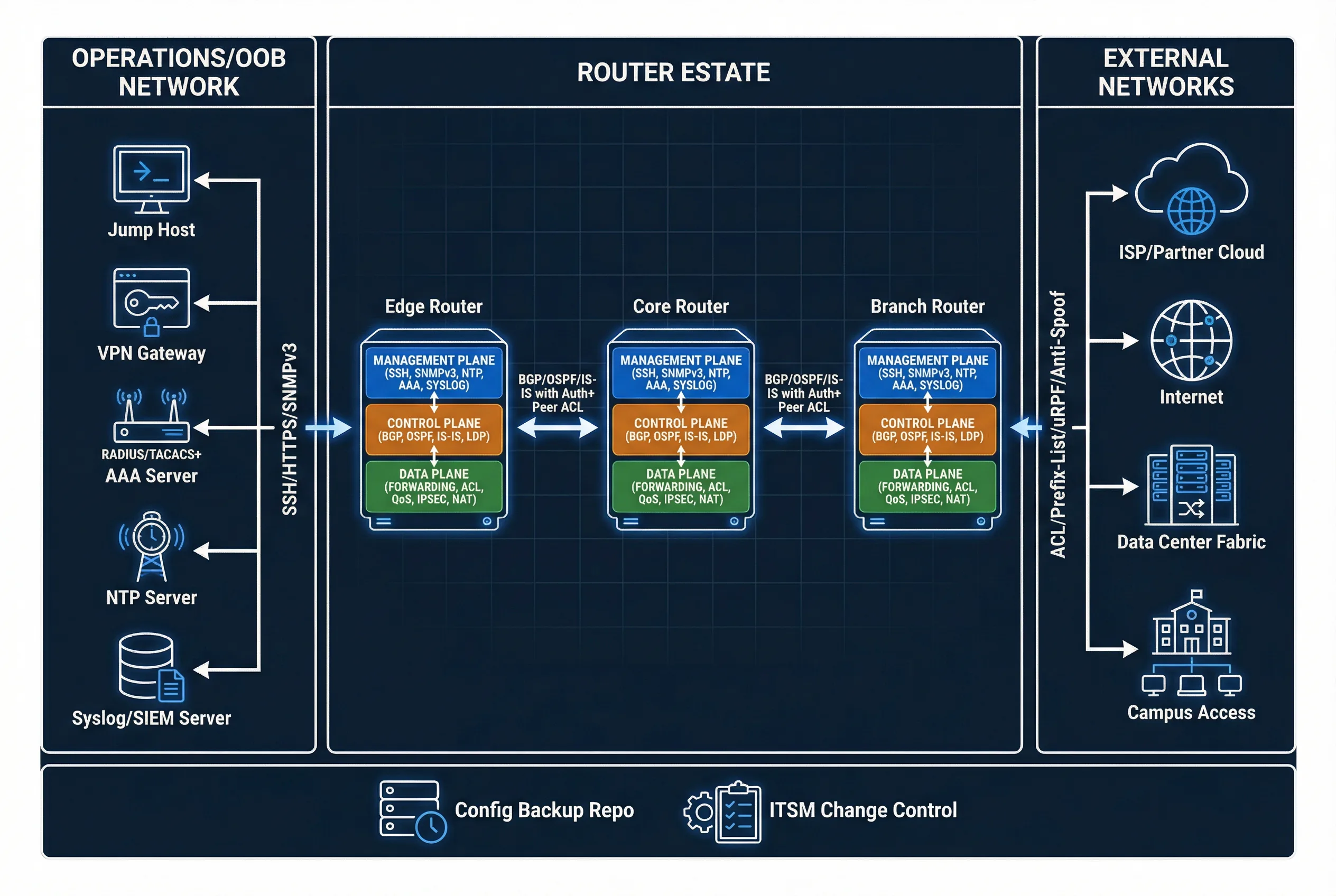
Key flows include the control flow (admin → jump host → SSH/HTTPS → router → AAA decision → command accounting to SIEM), the routing control flow (neighbor establishment only from trusted IP/interface with authenticated sessions and route policy filters), and the data flow (packets forwarded only if matching minimal-permit policy and anti-spoof checks).
Main Functions
The guide addresses nine core functional areas, each with clear implementation requirements and acceptance criteria. These functions collectively enforce the security baseline across all three router planes, ensuring that every administrative action is authenticated, every routing decision is policy-controlled, and every forwarding decision is validated against anti-spoofing rules.
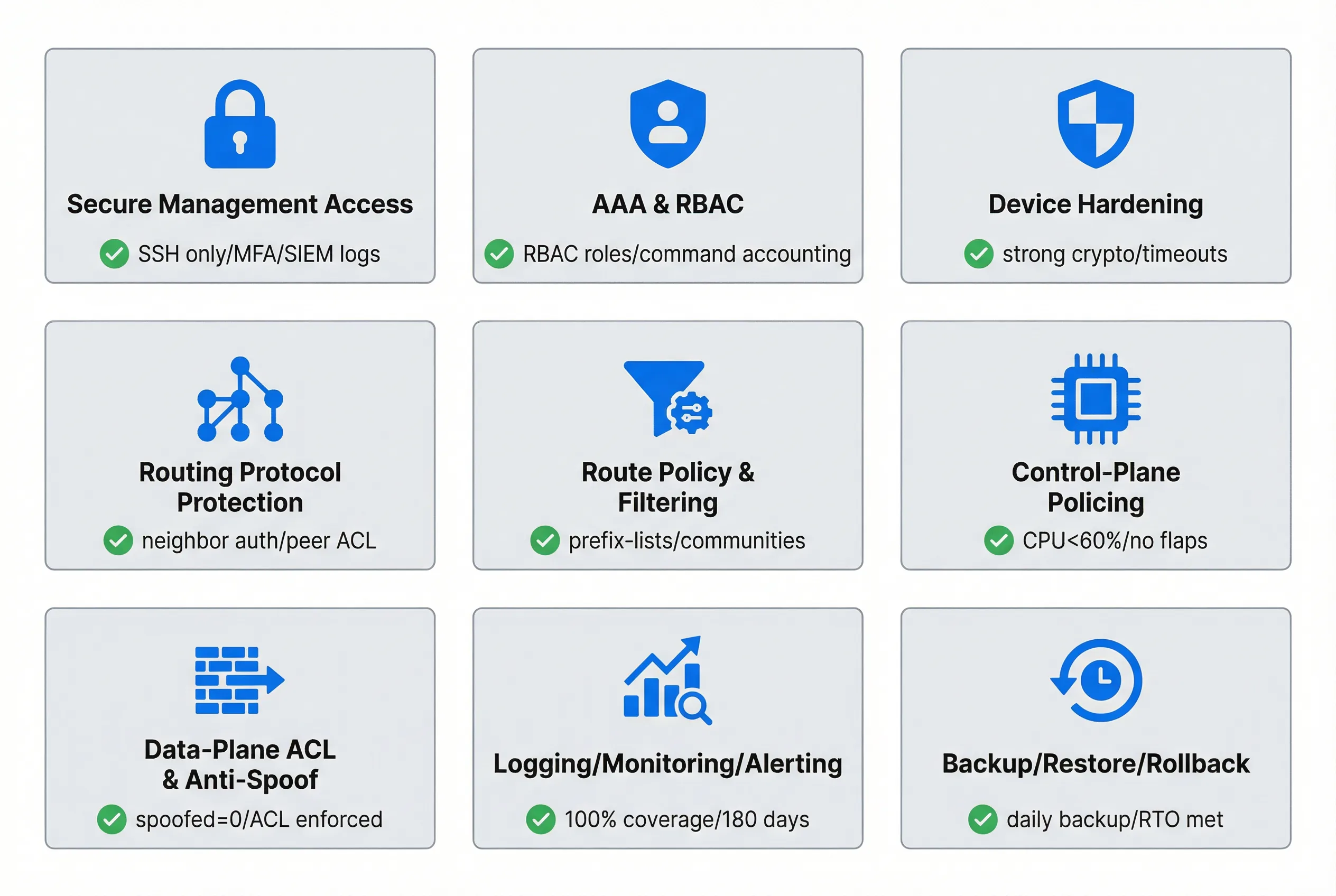
- Management-plane minimization: Allow only SSH/HTTPS from operations subnets/VRF; disable all legacy services.
- AAA + privilege separation (RBAC): Centralized auth, per-role authorization, command accounting, break-glass local account.
- Secure device baseline: Strong crypto, secure banners, session timeouts, lockouts, config integrity checks.
- Routing protocol hardening: Neighbor/interface/source whitelist, authentication, route policy (prefix-lists/communities), RPKI where applicable.
- Control-plane protection (CoPP/CPP): Rate limit and classify punts to CPU; drop abnormal floods.
- Data-plane boundary enforcement: Ingress/egress ACL, anti-spoof (uRPF), segmentation with VRF and policy routing.
- Auditability and recoverability: Versioned backups, signed configs (optional), change approval and rollback playbooks.
Chapter Navigation
This guide is organized into twelve chapters, each addressing a distinct aspect of router security configuration. Navigate directly to any chapter using the cards below or the left sidebar menu.